Forensic
BBI
Your GatewayTo Digital Justice
For individuals,
organisations, and
legal practitioners.
Our Solutions
Computer & Hard Drive Forensics
Comprehensive disk forensics covering HDDs, SSDs, USB drives, and RAID arrays.
Computer & Hard Drive Forensics
Comprehensive disk forensics covering HDDs, SSDs, USB drives, and RAID arrays.
Mobile Device Forensics
Full extraction and analysis of Android and iOS devices.
Mobile Device Forensics
Full extraction and analysis of Android and iOS devices.
Network & Cloud Forensics
Packet capture analysis, firewall log correlation, cloud storage forensics.
Network & Cloud Forensics
Packet capture analysis, firewall log correlation, cloud storage forensics.
Malware Analysis & Reverse Engineering
Static and dynamic malware analysis using sandbox environments.
Malware Analysis & Reverse Engineering
Static and dynamic malware analysis using sandbox environments.
Incident Response & Triage
24/7 rapid response for active security incidents.
Incident Response & Triage
24/7 rapid response for active security incidents.
Penetration Testing
Black-box, white-box, and grey-box penetration testing.
Penetration Testing
Black-box, white-box, and grey-box penetration testing.
OSINT & Threat Intelligence
Open-source intelligence gathering, dark web monitoring, and threat actor profiling.
OSINT & Threat Intelligence
Open-source intelligence gathering, dark web monitoring, and threat actor profiling.
Vulnerability Assessment & Security Audit
Systematic identification and risk-rated classification of security vulnerabilities.
Vulnerability Assessment & Security Audit
Systematic identification and risk-rated classification of security vulnerabilities.
Expert Witness Testimony
Our founder and lead investigators are qualified to provide expert witness testimony.
Expert Witness Testimony
Our founder and lead investigators are qualified to provide expert witness testimony.
Explore our
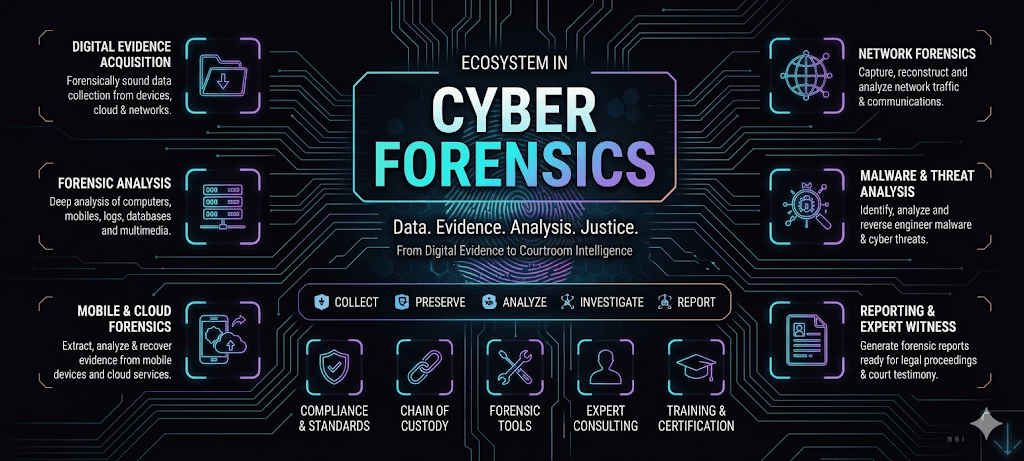
The Ecosystem
behind Byte Breach
Stay updated on our product ecosystem - from sub-products to integrations to AI models, & way more!
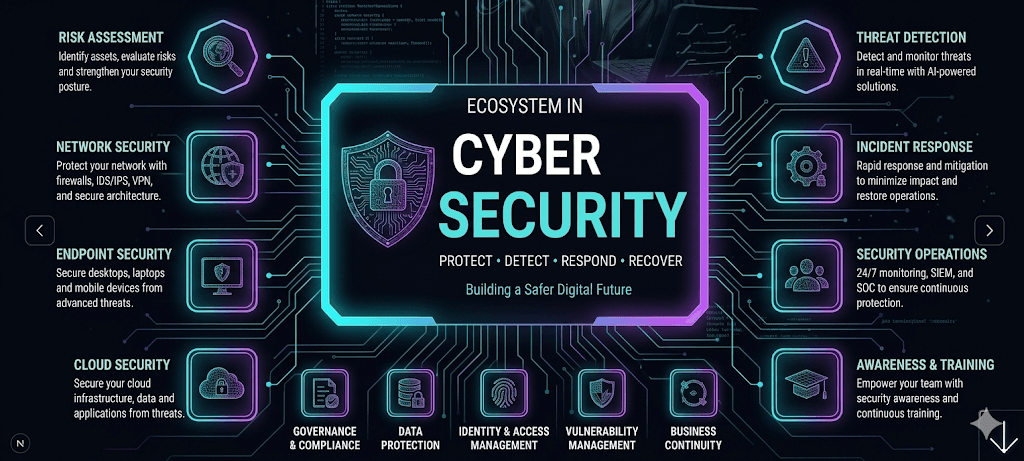
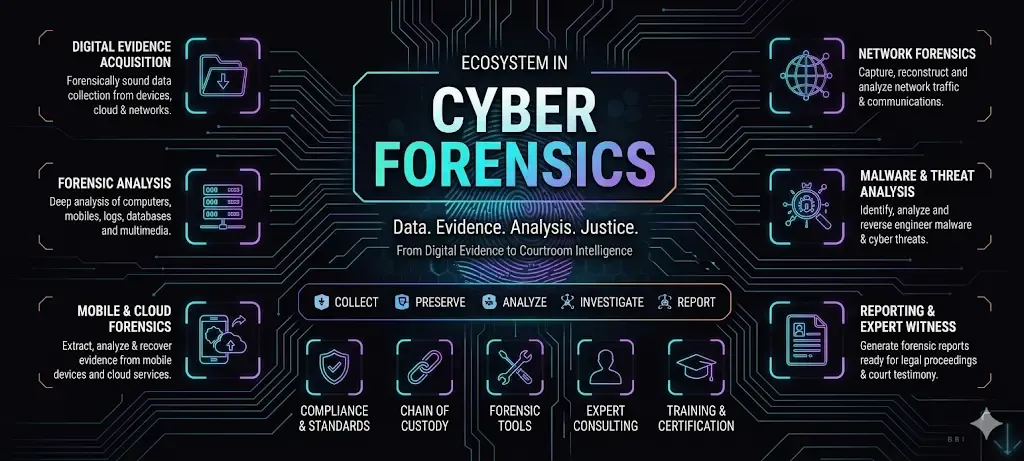
Digital Forensics & Cyber Security Layer
Data. Evidence. Analysis. Justice. From Digital Evidence to Courtroom Intelligence.
AI Utility & Services Layer
Advanced AI tooling for accelerated investigations and deeper insights.
Core Infrastructure Layer
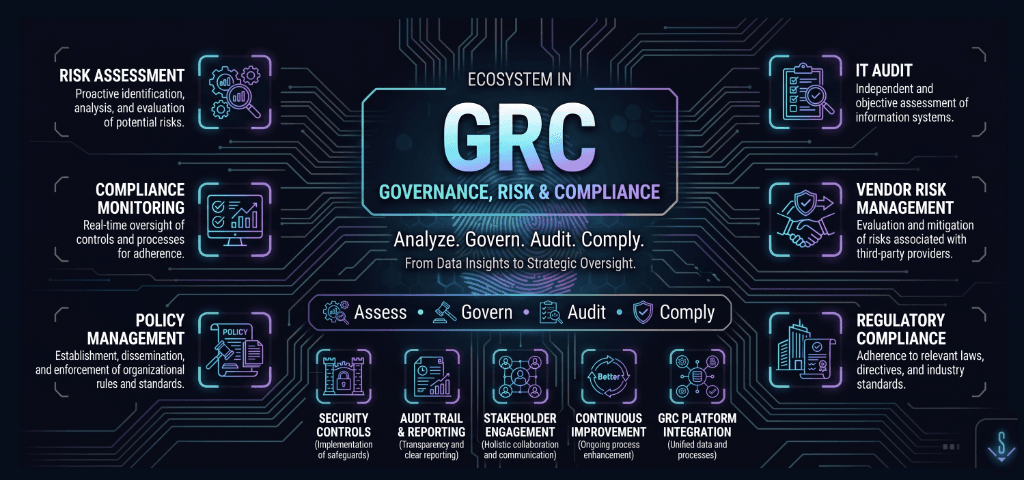
Analyze. Govern. Audit. Comply. From Data Insights to Strategic Oversight.
Growth & Incubation Layer
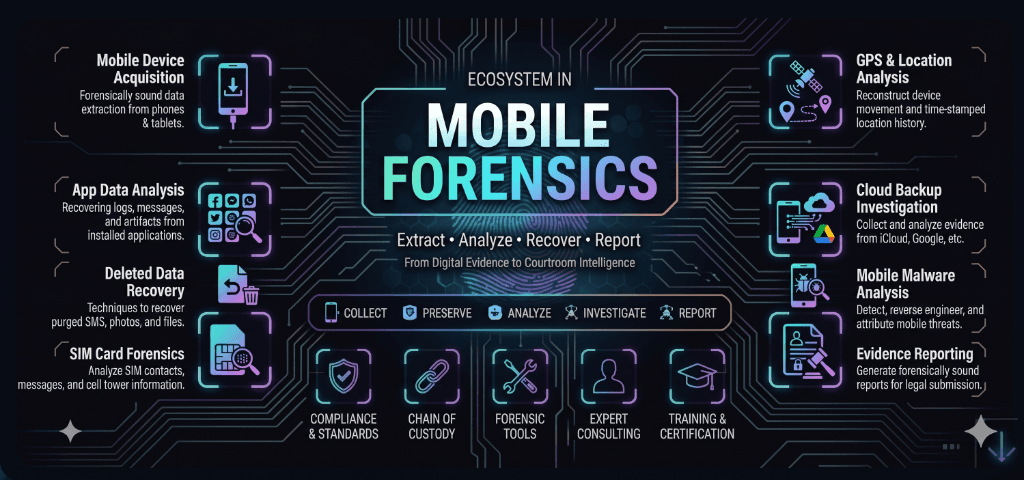
Extract • Analyze • Recover • Report. From Digital Evidence to Courtroom Intelligence.
Growth Layer
Detect • Investigate • Contain • Recover. A proactive and rapid cyber defense strategy.

Incubation Layer
Identify • Reverse • Understand • Mitigate.
OurPricing
Byte Breach Investigations offers transparent, case-based pricing for all digital forensics and cybersecurity services. All engagements include a free initial consultation and court-admissible documentation.
Free Consultation
Disk & Drive Forensics
Mobile Device Forensics
Malware Analysis
Incident Response
Penetration Testing
Academy Courses
HACKBOX Toolkit
OurPricing
Byte Breach Investigations offers transparent, case-based pricing for all digital forensics and cybersecurity services. All engagements include a free initial consultation.
Free Consultation
Disk & Drive Forensics
Mobile Device Forensics
Malware Analysis
Incident Response
Penetration Testing
Academy Courses
HACKBOX Toolkit
FacesbehindByte Breach
Learn more about our core team, and get familiar with our partners & advisors
Karthick Sekar

partners & projects (184)
Explore our
Roadmap
This is a short version of our roadmap.
Read full version here
- Identify all devices and storage media at the scene.
- Determine the scope and type of investigation.
- Document the initial state of digital assets.
- Assess jurisdiction and legal authority.
- Define evidence custodian and chain of custody protocols.
- Acquire bit-for-bit disk images using validated tools.
- Collect volatile data (RAM, running processes, open connections).
- Preserve original evidence with write-blockers.
- Document hardware serials and device configurations.
- Capture network traffic and log files.
- Generate cryptographic hash values (MD5/SHA-256) for all images.
- Store evidence in tamper-evident containers.
- Maintain strict chain of custody documentation.
- Create verified backups of all forensic images.
- Ensure secure storage with controlled access.
- Extract and categorise file system artefacts.
- Recover deleted files and fragmented data.
- Analyse registry entries, logs, and metadata.
- Examine email headers and web browser history.
- Process encrypted containers and password-protected files.
- Timeline reconstruction of user and system activities.
- Malware reverse engineering and behavioural analysis.
- IP geolocation and network attribution.
- Correlation of artefacts across multiple devices.
- Identify indicators of compromise (IoCs) and attack patterns.
- Maintain a detailed forensic examination log.
- Capture screenshots and annotate significant artefacts.
- Draft preliminary and final technical reports.
- Document tool versions, hashes, and examination environments.
- Prepare exhibits for legal proceedings.
- Prepare court-admissible expert witness reports.
- Create executive summaries for non-technical stakeholders.
- Develop visual timelines and evidence maps.
- Provide expert testimony before judicial bodies.
- Conduct client de-brief sessions with remediation recommendations.
Frequently askedQuestions
Can't find an answer to your question?
Feel free to contact us.
DIGITAL
INVESTIGATIONS
Byte Breach provided the clarity we needed. Their professionalism and rapid response were instrumental in resolving a critical incident for our company.
View Post →
Byte Breach Investigations brings a rare combination of technical rigour and legal awareness to digital forensics in India. A team worth watching.
View Post →
The incident response speed and quality of reporting from Byte Breach is unmatched in the region. Highly recommended for enterprise engagements.
View Post →
Byte Breach provided the clarity we needed. Their professionalism and rapid response were instrumental in resolving a critical incident for our company.
View Post →
Byte Breach Investigations brings a rare combination of technical rigour and legal awareness to digital forensics in India. A team worth watching.
View Post →
The incident response speed and quality of reporting from Byte Breach is unmatched in the region. Highly recommended for enterprise engagements.
View Post →